The internet is full of good and bad, we saw many people have put their efforts and tried their luck with the help of the internet and created milestones. For example, A Ugandan fashion designer is selling her clothing worldwide through the help of eCommerce, on the other side, the dark web is the biggest threat to the upcoming years for governments globally. Even, the rise of cybercrime and online frauds is a new threat for all of us including corporates and authorities worldwide.
Millions of people worldwide have received sextortion scam emails in 2020 asking for bitcoin. These bitcoin sextortion schemes sometimes include recipients’ passwords to make the threat more real. The authorities have advised what to do if you receive a bitcoin sextortion email.
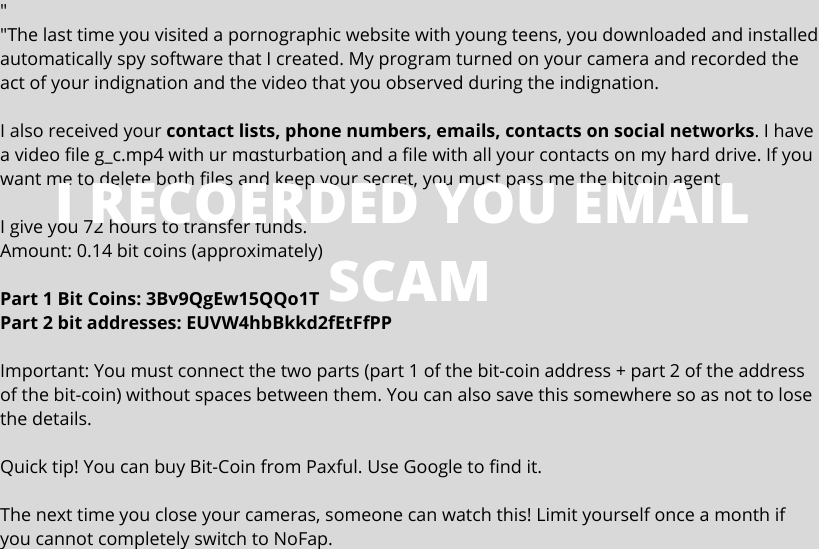
A new type of scam email had become quite prevalent recently, many people have received RECORDED YOU EMAIL containing an exact password of their computers and asking them for money. It can be quite alarming if you’re on the receiving end of it. It will contain a password that you either currently use or one that you have used in the past, and the email will usually try and scare you into sending money to the scammer. Typically the email will tell you that they have hacked your device and have a compromising video of you that they will send to your contacts if you don’t send them money, usually via bitcoin.
“Almost 300 million extortion scam emails were blocked by Symantec in the first five months of 2019.”
ad
What Is This, ‘I RECORDED YOU EMAIL SCAM?’
The number of people targeted by bitcoin sextortion scams in 2020 has increased rapidly. Most commonly, it is titled with I RECORDED YOU EMAIL is a common extortion (Sextortion) Scam involving phishing/email spoofing sent to unsuspecting victims where the criminals make various threats with demands for money in exchange to keep salacious, derogatory information (photos, videos) or other sensitive personal information they allegedly collected about you from being published or sent to family, friends, social media contacts, etc. The scammers may claim they know your password, hacked your computer, webcam, and/or email account. For more information about how these scams work, please read Beware of Phony Emails, Phone Calls & Tech Support Scams.
It’s important not to panic if you receive one of these emails, as they usually contain a tight deadline in order to try and force you to act quickly.
Examples of I Recorded You Sextortion Emails 2020
Sextortion is a widely used form of online blackmail where a cyber scammer threatens to reveal intimate images or videos of someone online — often to their friends, family, work colleagues, or social media lists — unless they pay a ransom quickly. The scammer often asks for payment in cryptocurrency, particularly bitcoin.
A sextortion mail scammer may claim to have compromised your computer, or other electronic devices, asking you that ‘I recorded you on your webcams watching sexual content. “I know pretty much everything about you. Your entire Facebook contact list, phone contacts along with all the online activity on your computer including your computer password,” the scammer may write. Another sextortion mail may say: “the last time you went to see porn material on webpages, my spyware was activated inside your personal computer which ended up logging lovely video footage of your masturbation simply by activating your cam.”
Sophos also provided some examples, such as “We made a video of you on a porn site with the screenshots and the webcam footage side-by-side” and “We also used this malware to film you via your webcam and to take screenshots of your browser.” SophosLabs security researcher Tamás Kocsír pointed out:
Other than email, sextortion can occur on a number of social network platforms, such as Facebook Messenger, Whatsapp, Telegram, Skype, Kakaotalk, Line, and WeChat. In particular, Whatsapp sextortion schemes have been gaining popularity recently. On these platforms, someone can befriend you and ask for selfies or sexy videos of you which can then be used to blackmail you with.
To make the threat more real, some sextortion mail may include your full or partial passwords as proof that there is actually malware on your computers.
How Scammers Get My Passwords?
When you see your password in the email, your first reaction is that you must have been hacked in some way. However, the way that the scammers obtain your email address and password are far less sophisticated than you might suspect. Unfortunately, there have been (and always will be) multiple occasions where criminals have extracted data from sources such as online forums, online stores, and even banks. In some of these breaches, usernames and passwords have been compromised and made publicly available for scammers to use. You can find out if any of your data has ever been compromised by entering your email address at a website called have I been pwned? It’s worth noting that you’ll need to check all of the email addresses that you use to sign up for various accounts online.
Scammers then use the email addresses and password combinations that were obtained during the data breach to send a wave of spam emails. This is why the password you see in the email might be a password you have since changed – they only have access to the data that was available at the time of the breach. If you have since changed your password, their data is effectively worthless.
What To Do On An Immediate Effect?
If the password in the email is one you currently use for anything, change it immediately. After this, you should run a virus and malware scan on your devices. It’s unlikely that you’ve been compromised (they probably wouldn’t email you to tell you because they’d lose access), but it’s always a good practice in these situations.
However, anyone receiving a sextortion scam mail should know that scammers typically have no compromising information about them.
Do not reply to the I RECORDED YOU EMAIL or any similar type, you should just ignore it. These emails are sent out to thousands of email addresses in the hope that they will either get a response or the recipient will send the ransom. If you respond, you’ll likely receive further communication to try and persuade you to send money. It’s always worth changing your passwords and virus/malware scanning your devices if you suspect you have been compromised in any way, but there’s no need to do anything else at this stage.
“It’s all a bluff,” Ducklin believes, asserting that the people behind sextortion email scams “don’t have malware on your computer, don’t have a video of you doing anything, don’t have screenshots of your browsing habits, and haven’t just stolen a list of your friends and family to send their non-existent video to.”
The U.K. National Crime Agency has advised how to deal with bitcoin sextortion scams. The organization recommends you report the scam to the police, do not pay any money, stop communicating with the person immediately, report the scam to your internet service provider, and take screenshots with as much information as possible for evidence. Californian District Attorney Jeff Reisig also advised what to do if you get a sextortion mail. He emphasized:
How To Protect Me In The Future From I RECORDED YOU EMAIL Or Similar Scams?
There’s nothing you can do to prevent your data from being compromised in a third-party breach, but you can take steps to protect yourself if it does happen.
- Use 2-factor authentication where possible.
- Do not re-use passwords for multiple accounts – try and use different passwords for every single login you use.
- Use strong passwords. Use all the characters available – lowercase letters, uppercase letters, numbers, and special characters.
- Use passwords that are not easy to guess. Pa55word! uses all the characters available, but is still very easy to guess.
- Do not store your passwords in plain text.
- Use a password manager if you can. A password manager can securely store your usernames and passwords for all the services you use that require a login. You just need to remember one password to access the password manager, which makes it easier to use much stronger passwords that you never have to remember. Just make sure you use a very strong password to access the password manager and never write it down or use it for any other login. LastPass and KeePassXC are both free and commonly used managers, but there are other solutions that you can use too.
- Change your passwords on a regular basis. This will ensure that if your username and password are compromised, it can’t be used for very long.
- Do You Suspect Your Computer May Be Infected with ‘I RECORDED YOU!’ Email Scam & Other Threats? Scan Your Computer for Threats with SpyHunter
- As with other phishes, our advice is not to engage with the phisher, forward the email to report@phishing.gov.uk which is the NCSC’s Suspicious Email Reporting Service (SERS), and then delete it. (FOR UK CITIZENS ONLY)
Quick Facts About This Email Scam
The cybersecurity firm found that 81% of the millions of sextortion scam messages it analyzed were in English, 10% in Italian, 4% in German, 3.5% in French, and 1.2% in Chinese.
ad




Comments are closed.